Points to take note:
- The following screenshots are taken on K2 Core 4.1 VM with blackpearl 4.5 Update KB001420.
- Exchange2010 and Blackpearl are installed on the same machine.
- The logged in user is denallix\administrator.
- Pre-requisites: http://help.k2.com/kb001189.aspx
- KB001189 quotes you need a second service account. This is not compulsory and I have used K2 service account to do all the operations. So only one account is sufficient.
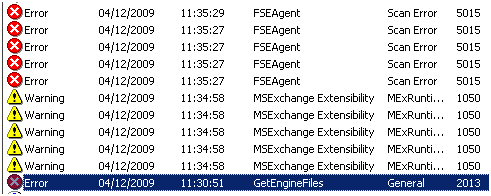
- All the errors start with “Please make sure the K2 service account has impersonation rights in Exchange” This is a misleading message, so ignore that bit and look for the text after that.
=========================================================================================
Option 1: Set Authentication Mode to ServiceAccount [DENALLIX\K2Service]

“DENALLIX\K2Service” is member of following AD roles:

With the settings in place, we can create a meeting “On Behalf Of” any user as shown in the next 3 screenshots



Error: The SMTP address has no mailbox associated with it.
Cause: This happens if the “On Behalf Of” field has an invalid email address or the email is not found in Exchange

Error: The SMTP address format is invalid.
Cause: This happens if the “On Behalf Of” field does not have a value in the format of a valid email address


=========================================================================================
Option 2: Set Authentication Mode to Impersonate [Enforce Impersonation is unchecked]

The following Exchange Management Shell screenshot shows “DENALLIX\K2Service” is part of Exchange’s ApplicationImpersonation role. This was done during installation by the K2 setup manager.
Get-ManagementRoleAssignment –Role “ApplicationImpersonation”

If you want to know more about Role Based Access Control (RBAC), please check this: http://www.msexchange.org/articles_tutorials/exchange-server-2010/management-administration/exchange-2010-role-based-access-control-part1.html
With the above settings in place, we can create a meeting “On Behalf Of” any user as shown in the next 2 screenshots. The smartobject tester tool is running under the context of logged in user denallix\administrator


=========================================================================================
Option 3: Set Authentication Mode to Impersonate and check “Enforce Impersonation”

Since the logged in user is denallix\administrator, the Smartobject tester tool ran using those credentials:

Error: The account does not have permission to impersonate the requested user.
Cause: ‘denallix\administrator’ account is not part of Exchange’s ApplicationImpersonation role

Resolution:
new-ManagementRoleAssignment –Name “_suImpersonateRoleAsg” –Role “ApplicationImpersonation” –User “administrator@denallix.com”
Note: After executing the new-ManagementRoleAssignment powershell cmdlet, you must wait 5-10 minutes (depends on exchange setup) for the smartobject to pick up those changes.

After waiting for the exchange role refresh, you should be able to create the meeting with Enforce Impersonation enabled.

=========================================================================================
Option 4: ‘Run as different user’ option to launch Smartobject tester tool, Set Authentication Mode to Impersonate and check “Enforce Impersonation”

The error is same as explained previously. But if you try to execute the new-ManagementRoleAssignment powershell cmdlet, you will get an error as below:

This is due to the usage of same name “_suImpersonateRoleAsg” in the command. So delete the existing entry and then add the user to the role.
Remove-ManagementRoleAssignment “_suImpersonateRoleAsg”

The above screenshot confirms that _suImpersonateRoleAsg role will be removed which has Administrator as the member. Since the role has now been deleted, you can add “Run as” user to the exchange role.

As mentioned earlier, you must wait 5-10 minutes before trying to create the meeting request.